OWASP Top 10: What are them and how to prevent them
Open Web Application Security Project, or OWASP is an online community of people who care about web application security (like you and I), and they provide several recommendations to prevent many sorts of online attacks.
This is an hour-long session (with 15 minute Q&A) that we go through the possible security vulnerabilities, and how we can prevent them. The focus is on PHP language, but the concepts are all the same. PHP 7, 7.1 and 7.2 were released with several feature that can help us with security tightening too, and the PHP 7.3 that is just around the corner will have a few more tricks up its sleeve too!
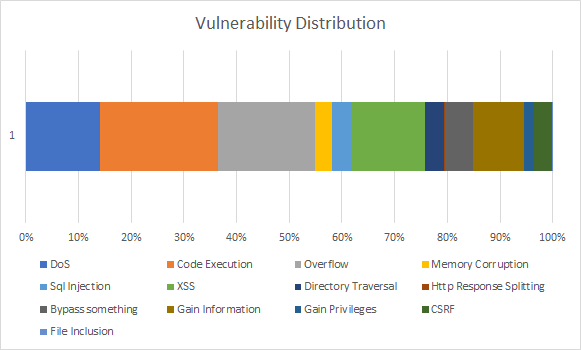
We will also talk about which type of attacks are most common using historical data of CVEs.
CMSs such as Drupal and WordPress provide built-in features that helps us prevent some of these attacks, such as XSS and CSRF (don't worry if these abbreviations make sense, because we will explain them in the talk too!) protection with various approaches. For each of the vulnerability type we talk about, we will take a look at these built-in protection mechanisms as well as how to implement them in pure PHP.
Lastly, we will take a look at some of the recent vulnerabilities, what went wrong, and the rationale behind each of these fixes.
OWASP Top 10 is a vastly widespread topic to cover in a 45 minute session, so this talk will only go through the general ideas and the prevention approaches. It will not make you a security expert at the end of the session, but it will definitely make you aware of these possible vulnerabilities, and how to approach each of them no matter what framework or programming language you use.
References
PDF | PPTX | View online